 Facebook
Facebook
 https://www.facebook.com/vanphongketnoi
https://www.facebook.com/vanphongketnoi
 Messenger
Messenger

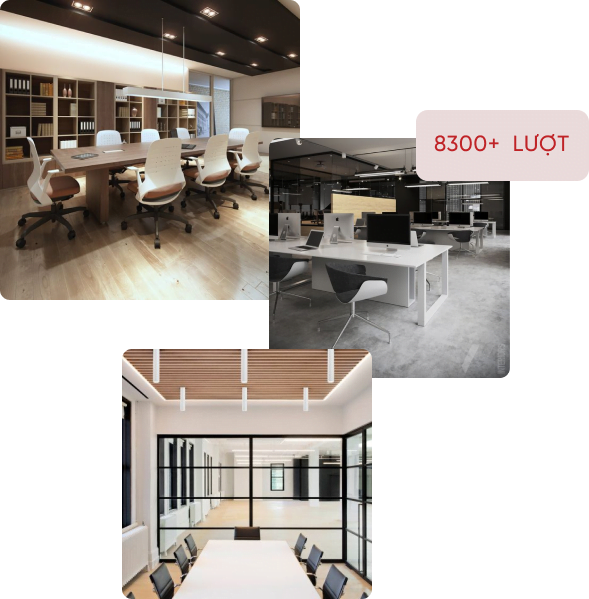
Văn phòng chung nhưng phong khách riêng. Bạn vừa có thể tận dụng không gian chung đầy sáng tạo lại vừa có không gian riêng đậm bản sắc của doanh nghiệp. Trang bị thiết bị hiện đại và tiện nghi luôn sẵn sàng đáp ứng nhu cầu của bạn.

Không gian mở, thoáng đãng với nhiều cửa sổ đón ánh nắng tự nhiên. Không chỉ là nơi làm việc, không gian tại Co Office còn giúp bạn thư giãn, khơi nguồn cảm hứng sáng tạo giúp năng suất làm việc hiệu quả hơn.


– Văn phòng ảo: Tiện ích chung hiện đại, (trang thiết bị văn phòng,…), địa chỉ thuận lợi (phù hợp đăng ký kinh doanh, giao nhận bưu phẩm,…)
– Văn phòng chia sẻ: Đầy đủ tiện nghi và linh hoạt thay đổi, sáng tạo theo nhu cầu.
– Phòng làm việc riêng: Thiết kế chuyên nghiệp và trang bị đầy đủ thiết bị hiện đại để tự do thể hiện cá tính, phong cách làm việc riêng
– Phòng họp, sự kiện lớn: Không gian rộng rãi với đầy đủ trang thiết bị chất lượng cao đáp ứng mọi nhu cầu.
– Các dịch vụ tiện lợi khác: Tiếp nhận thư/bưu phẩm; Tư vấn dịch vụ thành lập doanh nghiệp miễn phí; Dịch vụ kế toán, BHXH cho doanh nghiệp,…
Dù đã “bình thường mới”, an toàn sức khoẻ vẫn là ưu tiên hàng đầu. CO OFFICE luôn tuân thủ nghiêm ngặt mọi quy định về Phòng chống COVID-19 để đảm bảo cho bạn và đồng nghiệp, đối tác có không gian làm việc an toàn nhất

– Đảm bảo tuân thủ chỉ thị 5K.
– Đảm bảo tất cả mọi người đều khai báo y tế đầy đủ trước khi vào CO OFFICE.
Yêu cầu tất cả mọi người ra vào và làm việc tại CO OFFICE đều phải đeo khẩu trang.
– Thực hiện giãn cách 2M ở tất cả không gian chung.
– Tăng cường diệt khuẩn bằng dung dịch khử khuẩn, lau chùi các bề mặt và các điểm tiếp xúc chung tại khu vực chung, tất cả tay nắm cửa ra vào tại các phòng, không gian chung và phòng riêng, nhà vệ sinh.
– Luôn cập nhập thông tin về tình hình phòng chống COVID-19 trên các kênh truyền thông của CO OFFICE.


VĂN PHÒNG CHUNG, NHƯNG PHONG CÁCH RIÊNG
Với CO OFFICE, bạn sẽ vừa có không gian riêng làm việc riêng đậm bản sắc, vừa toàn quyền sử dụng miễn phí các không gian chung đầy sáng tạo – điều mà một văn phòng truyền thống không thể có
Phong cách chuyên nghiệp, thái độ thân thiện của đội ngũ Lễ tân không những giúp bạn bắt đầu ngày làm việc thật hứng khởi mà còn mang lại ấn tượng với các đối tác của bạn. Hơn nữa, bạn còn có cơ hội mở rộng kết nối với nhiều doanh nghiệp trẻ tại CO OFFICE.
VĂN PHÒNG ĐẸP – TIỆN NGHI – HIỆN ĐẠI TRONG TẦM TAY
Với vị trí đắc địa tại Quận 7, CO OFFICE là giải pháp văn phòng toàn diện đa chức năng, đáp ứng đầy đủ nhu cầu làm việc, gắn kết và chăm sóc nhân viên của doanh nghiệp với mức chi phí tối ưu nhất.
Lựa chọn CO OFFICE là cách để bạn có văn phòng Đẹp – Tiện nghi – Hiện đại với chi phí vô cùng tiết kiệm.

Các bàn làm việc được cố định hoặc có thể linh hoạt thay đổi, sáng tạo theo nhu cầu

Đặt phòng họp theo giờ với đầy đủ trang thiết bị chất lượng cao, sẵn sàng đáp ứng kịp thời các yêu cầu phát sinh

Không gian mở, đầy đủ tiện nghi giúp bạn thư giãn, tinh thần thoải mái cho ngày làm việc hiệu quả

Được thiết kế theo mong muốn của bạn để phù hợp với bản sắc, văn hóa của doanh nghiệp
Copyright © 2020 CO Office. All rights reserved.